Zero-Touch Deployment: A cornerstone of modern device management
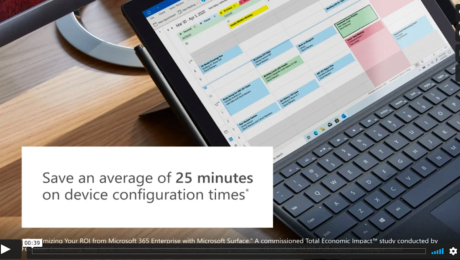
Don’t deploy without your organization’s security protocols in place. By leveraging features built into Windows 10, along with a variety of complementary cloud-based services and capabilities, Microsoft makes deployment simple. With “zero-touch,” Surface devices go from factory-sealed to work-ready in a matter of minutes.
Learn how Zero-Touch deployment is a critical component of Microsoft’s innovative approach to endpoint management across the entire device lifecycle.
Read the guide to learn more.
View: Zero-Touch Deployment: A cornerstone of modern device management
- Published in Technology
How Starbucks is using AI to improve the customer experience
At Microsoft’s Build conference, Starbucks showed how artificial intelligence is helping them better predict what customers may be in the mood for by considering such factors such as weather, location, and user preferences.
- Published in Technology
Shipping company navigates to the cloud, boosts security, cuts operating costs by 50%
Qatari shipping and maritime company Nakilat has one of the world’s largest fleets of liquefied natural gas (LNG) carriers, transporting LNG from Qatar to global markets. To increase its competitive advantage, Nakilat wanted to improve employee productivity and mobility, without compromising on data security. It uses Microsoft 365 and Microsoft Cloud App Security to deliver highly secure cloud-first workplaces—shipboard and in the office. Nakilat also adopted the Microsoft Azure platform to optimize its operations and improve business continuity, reducing operating costs by 50 percent. See more in this video.
- Published in Technology
Three important information security predictions for 2020
As digital transformation evolves with each passing year, so too does the information security landscape. For organizations that leverage cloud technology, this means staying updated on new ways to prevent and counter cybersecurity threats while relying on trustworthy sources of information for insights into future potential security developments and circumstances.
In this article, you’ll learn about three critical cybersecurity predictions for 2020, the impact each may have on the digital business landscape, and how your business can act to avoid being affected.
- Published in Technology
Microsoft Threat Protection stops attack sprawl and auto-heals enterprise assets with built-in intelligence and automation
Attackers will cross multiple domains like email, identity, endpoints, and applications to find the point of least resistance. Today’s defense solutions have been designed to protect, detect, and block threats for each domain separately, allowing attackers to exploit the seams and threshold differences between solutions—leaving the business vulnerable to attack. Microsoft Threat Protection stops attack sprawl and auto-heals enterprise assets with built in intelligence and automation. Read on to learn more.
- Published in Technology
Leveraging Tech to Improve Customer Experience: 11 Smart Techniques
The importance of customer experience has taken off in recent years. As competition becomes the norm in many digital and application spaces, the interaction that the consumer has with a company becomes more important. CX is vital in helping a company retain its customers and grow its customer base through organic referrals.
Luckily, technology offers several ways for businesses to improve their customer experience. In this article, 11 members of the Forbes Technology Council explain some techniques businesses can use to improve their customers’ experience.
- Published in Technology
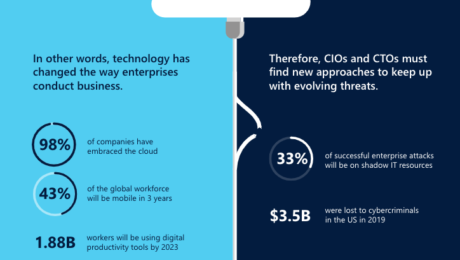
6 risks and opportunities of the intelligent, connected cloud
No technology is a hundred percent failproof, and as businesses get more and more digitalized, they’re also unwillingly increasing the risk of someone stealing their data or compromising their credibility. Therefore, before taking their business to the cloud, organizations must carefully choose the platforms that ensure the safety and compliance of their data while enabling them to seize the opportunities available to them.
In this infographic, you’ll catch a glimpse of both sides of cloud technology: on one hand, the immense opportunities it provides in terms of innovation and mobility; and on the other, the risks that businesses must be aware of to safeguard the continuity of their operations in the digital world.
View: 6 risks and opportunities of the intelligent, connected cloud
- Published in Technology
Secure from deployment to decommission
Don’t deploy without your organization’s security protocols in place. Reduce IT complexity and deploy straight to employees with your security protocols in place. By leveraging features built into Windows 10, along with a variety of complementary cloud-based services and capabilities, Microsoft makes deployment simple.
With “zero-touch,” Microsoft Surface devices go from factory-sealed to work-ready in a matter of minutes. Keep data secure from a Surface device’s first deployment to its last, no matter how many times and under what circumstances it changes hands.
Watch this video to learn how Zero-Touch deployment is a critical component of Microsoft’s innovative approach to endpoint management across the entire device lifecycle.
Contact us today to learn more.
marketing@ralliton.com
+357 22029700
- Published in Technology
Greater Security
Greater security at lower cost with the expertise and power of Microsoft security solutions. Learn more about simplifying and fortifying with Microsoft security.
- Published in Technology
Drive security and compliance across the entirety of your business. Learn more about Microsoft 365.
Regardless of the nature of your organization, keeping your data secure and ensuring compliance are two of the most demanding priorities. After all, what good is creativity, efficiency, and talent if they can get easily stolen, copied, or shut down because of outdated technology?
The good news is that even though these requirements are as crucial as they’ve ever been, never before have businesses been vested with so many alternatives to customize the way they do business. In fact, the cloud has allowed organizations to shift their manpower from security and compliance to increasing productivity and innovation.
Subscribe now to learn about digital transformation success stories and how you can ensure your business remains secure and compliant with Microsoft.
- Published in Technology